![Cisco Secure Firewall Threat Defense Virtual Getting Started Guide, Version 7.2 and Earlier - Deploy the Threat Defense Virtual on AWS [Cisco Secure Firewall Threat Defense Virtual] - Cisco Cisco Secure Firewall Threat Defense Virtual Getting Started Guide, Version 7.2 and Earlier - Deploy the Threat Defense Virtual on AWS [Cisco Secure Firewall Threat Defense Virtual] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/400001-500000/450001-460000/457001-458000/457812.png)
Cisco Secure Firewall Threat Defense Virtual Getting Started Guide, Version 7.2 and Earlier - Deploy the Threat Defense Virtual on AWS [Cisco Secure Firewall Threat Defense Virtual] - Cisco

What is a Leacky bucket syndrome for business? Most businesses do not even realise that they are into a leaky bucket scenario. Learn More..
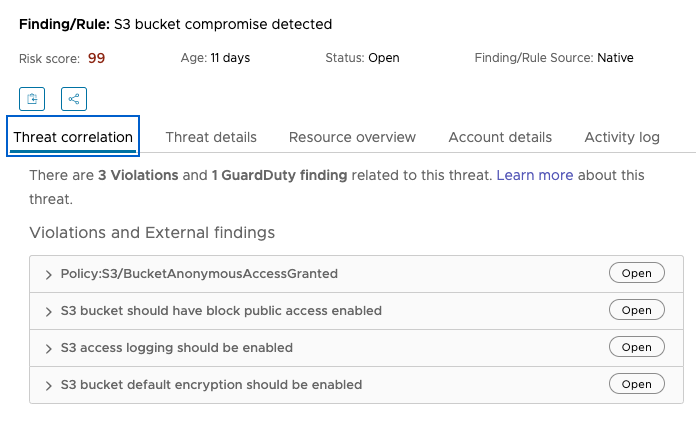
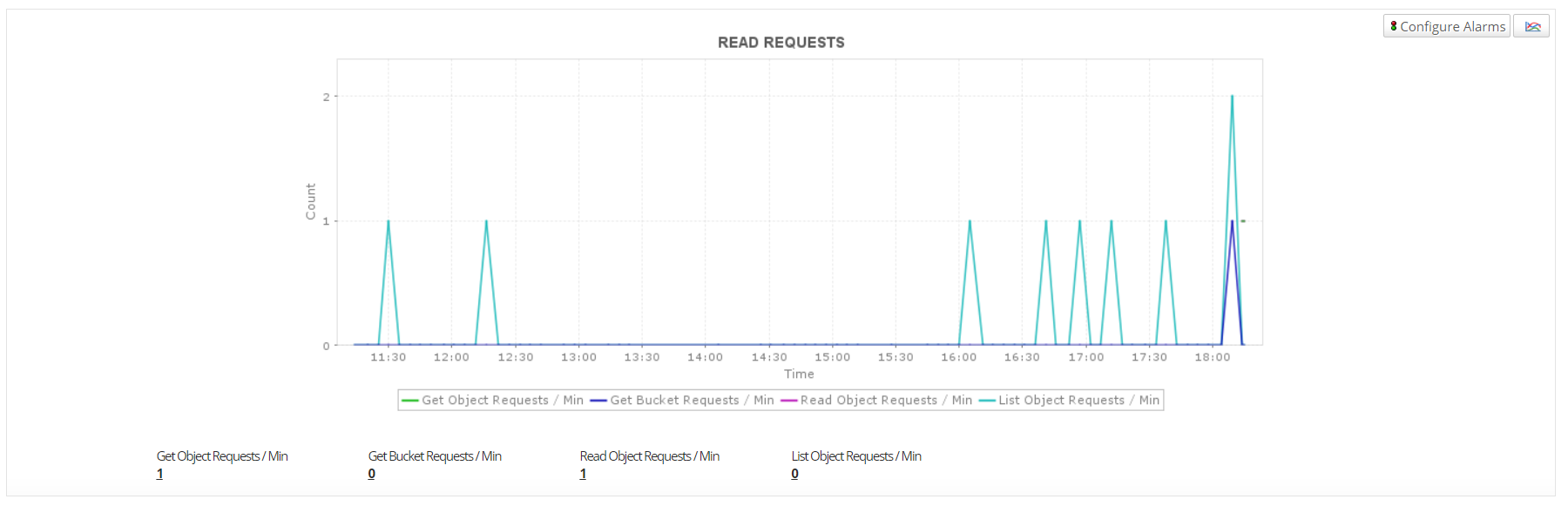
Investigate findings from CloudHealth Secure State to discover and close vulnerabilities in your organization
![Cisco Secure Firewall Threat Defense Virtual Getting Started Guide, Version 7.2 and Earlier - Deploy the Threat Defense Virtual on AWS [Cisco Secure Firewall Threat Defense Virtual] - Cisco Cisco Secure Firewall Threat Defense Virtual Getting Started Guide, Version 7.2 and Earlier - Deploy the Threat Defense Virtual on AWS [Cisco Secure Firewall Threat Defense Virtual] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/400001-500000/460001-470000/466001-467000/466030.jpg)
Cisco Secure Firewall Threat Defense Virtual Getting Started Guide, Version 7.2 and Earlier - Deploy the Threat Defense Virtual on AWS [Cisco Secure Firewall Threat Defense Virtual] - Cisco

Taking visible actions to sustainably manage groundwater resources in the decade of action | United Nations Development Programme
![Cisco Secure Firewall Threat Defense Virtual Getting Started Guide, Version 7.2 and Earlier - Deploy the Threat Defense Virtual on AWS [Cisco Secure Firewall Threat Defense Virtual] - Cisco Cisco Secure Firewall Threat Defense Virtual Getting Started Guide, Version 7.2 and Earlier - Deploy the Threat Defense Virtual on AWS [Cisco Secure Firewall Threat Defense Virtual] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/400001-500000/450001-460000/457001-458000/457809.png)
Cisco Secure Firewall Threat Defense Virtual Getting Started Guide, Version 7.2 and Earlier - Deploy the Threat Defense Virtual on AWS [Cisco Secure Firewall Threat Defense Virtual] - Cisco